The Network Time Protocol (NTP) is a networking protocol for clock synchronization between computer systems over packet-switched, variable-latency data networks. In operation since before 1985, NTP is one of the oldest Internet protocols in current use. NTP was designed by David L. Mills of the University of Delaware.
 | |
| International standard | RFC 5905 |
|---|---|
| Developed by | David L. Mills, Harlan Stenn, Network Time Foundation |
| Introduced | 1985 |
NTP is intended to synchronize all participating computers to within a few milliseconds of Coordinated Universal Time (UTC).[1]: 3 It uses the intersection algorithm, a modified version of Marzullo's algorithm, to select accurate time servers and is designed to mitigate the effects of variable network latency. NTP can usually maintain time to within tens of milliseconds over the public Internet, and can achieve better than one millisecond accuracy in local area networks under ideal conditions. Asymmetric routes and network congestion can cause errors of 100 ms or more.[2][3]
The protocol is usually described in terms of a client–server model, but can as easily be used in peer-to-peer relationships where both peers consider the other to be a potential time source.[1]: 20 Implementations send and receive timestamps using the User Datagram Protocol (UDP) on port number 123.[4][5]: 16 They can also use broadcasting or multicasting, where clients passively listen to time updates after an initial round-trip calibrating exchange.[3] NTP supplies a warning of any impending leap second adjustment, but no information about local time zones or daylight saving time is transmitted.[2][3]
The current protocol is version 4 (NTPv4),[5] which is backward compatible with version 3.[6]
History edit
RFC evolution for NTP | ||||||||||||||
1980 — – 1985 — – 1990 — – 1995 — – 2000 — – 2005 — – 2010 — – 2015 — – 2020 — – | v0, RFC 958[7] v1, RFC 1059[8] v2, RFC 1119[9] v3, RFC 1305[6] v4, RFC 5905[5] v3, RFC 1361[10] v3, RFC 1769[11] v4, RFC 2030[12] v4, RFC 4330[13] |
| ||||||||||||
In 1979, network time synchronization technology was used in what was possibly the first public demonstration of Internet services running over a trans-Atlantic satellite network, at the National Computer Conference in New York. The technology was later described in the 1981 Internet Engineering Note (IEN) 173[18] and a public protocol was developed from it that was documented in RFC 778. The technology was first deployed in a local area network as part of the Hello routing protocol and implemented in the Fuzzball router, an experimental operating system used in network prototyping, where it ran for many years.
Other related network tools were available both then and now. They include the Daytime and Time protocols for recording the time of events, as well as the ICMP Timestamp messages and IP Timestamp option (RFC 781). More complete synchronization systems, although lacking NTP's data analysis and clock disciplining algorithms, include the Unix daemon timed, which uses an election algorithm to appoint a server for all the clients;[19] and the Digital Time Synchronization Service (DTSS), which uses a hierarchy of servers similar to the NTP stratum model.
In 1985, NTP version 0 (NTPv0) was implemented in both Fuzzball and Unix, and the NTP packet header and round-trip delay and offset calculations, which have persisted into NTPv4, were documented in RFC 958. Despite the relatively slow computers and networks available at the time, accuracy of better than 100 milliseconds was usually obtained on Atlantic spanning links, with accuracy of tens of milliseconds on Ethernet networks.
In 1988, a much more complete specification of the NTPv1 protocol, with associated algorithms, was published in RFC 1059. It drew on the experimental results and clock filter algorithm documented in RFC 956 and was the first version to describe the client–server and peer-to-peer modes. In 1991, the NTPv1 architecture, protocol and algorithms were brought to the attention of a wider engineering community with the publication of an article by David L. Mills in the IEEE Transactions on Communications.[20]
In 1989, RFC 1119 was published defining NTPv2 by means of a state machine, with pseudocode to describe its operation. It introduced a management protocol and cryptographic authentication scheme which have both survived into NTPv4, along with the bulk of the algorithm. However the design of NTPv2 was criticized for lacking formal correctness by the DTSS community, and the clock selection procedure was modified to incorporate Marzullo's algorithm for NTPv3 onwards.[21]
In 1992, RFC 1305 defined NTPv3. The RFC included an analysis of all sources of error, from the reference clock down to the final client, which enabled the calculation of a metric that helps choose the best server where several candidates appear to disagree. Broadcast mode was introduced.
In subsequent years, as new features were added and algorithm improvements were made, it became apparent that a new protocol version was required.[22] In 2010, RFC 5905 was published containing a proposed specification for NTPv4.[23] Following the retirement of Mills from the University of Delaware, the reference implementation is currently maintained as an open source project led by Harlan Stenn.[24][25] On the IANA side, a ntp (network time protocols) work group is in charge of reviewing proposed drafts.[26]
The protocol has significantly progressed since NTPv4.[23] As of 2022[update], three RFC documents describing updates to the protocol have been published,[5] not counting the numerous peripheral standards such as NTS (RFC 8915).[26] Mills had mentioned plans for a "NTPv5" on his page, but one was never published.[23] An unrelated draft termed "NTPv5" by M. Lichvar of chrony was initiated in 2020 and includes security, accuracy, and scaling changes.[27]
SNTP edit
As NTP replaced the use of the old Time Protocol, some use-cases nevertheless found the full protocol too complicated. In 1992, Simple Network Time Protocol (SNTP) was defined to fill this niche. The SNTPv3 standard describes a way to use NTPv3, such that no storage of state over extended periods of time is needed. The topology becomes essentially the same as with the Time Protocol, as only one server is used.[10] In 1996, SNTP was updated to SNTPv4[12] with some features of the then-in-development NTPv4. The current version of SNTPv4 is merged into the main NTPv4 standard in 2010.[5] SNTP is fully interoperable with NTP since it does not define a new protocol.[28]: §14 However, the simple algorithms provide times of reduced accuracy and thus it is inadvisable to sync time from an SNTP source.[13]
Clock strata edit
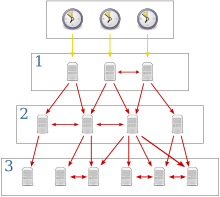
NTP uses a hierarchical, semi-layered system of time sources. Each level of this hierarchy is termed a stratum and is assigned a number starting with zero for the reference clock at the top. A server synchronized to a stratum n server runs at stratum n + 1. The number represents the distance from the reference clock and is used to prevent cyclical dependencies in the hierarchy. Stratum is not always an indication of quality or reliability; it is common to find stratum 3 time sources that are higher quality than other stratum 2 time sources.[a] A brief description of strata 0, 1, 2 and 3 is provided below.
- Stratum 0
- These are high-precision timekeeping devices such as atomic clocks, GNSS (including GPS) or other radio clocks, or a PTP-synchronized clock.[29] They generate a very accurate pulse per second signal that triggers an interrupt and timestamp on a connected computer. Stratum 0 devices are also known as reference clocks. NTP servers cannot advertise themselves as stratum 0. A stratum field set to 0 in NTP packet indicates an unspecified stratum.[30]
- Stratum 1
- These are computers whose system time is synchronized to within a few microseconds of their attached stratum 0 devices. Stratum 1 servers may peer with other stratum 1 servers for sanity check and backup.[31] They are also referred to as primary time servers.[2][3]
- Stratum 2
- These are computers that are synchronized over a network to stratum 1 servers. Often a stratum 2 computer queries several stratum 1 servers. Stratum 2 computers may also peer with other stratum 2 computers to provide more stable and robust time for all devices in the peer group.
- Stratum 3
- These are computers that are synchronized to stratum 2 servers. They employ the same algorithms for peering and data sampling as stratum 2, and can themselves act as servers for stratum 4 computers, and so on.
The upper limit for stratum is 15; stratum 16 is used to indicate that a device is unsynchronized. The NTP algorithms on each computer interact to construct a Bellman–Ford shortest-path spanning tree, to minimize the accumulated round-trip delay to the stratum 1 servers for all the clients.[1]: 20
In addition to stratum, the protocol is able to identify the synchronization source for each server in terms of a reference identifier (refid).
| Refid[32] | Clock Source |
|---|---|
| GOES | Geosynchronous Orbit Environment Satellite |
| GPS | Global Positioning System |
| GAL | Galileo Positioning System |
| PPS | Generic pulse-per-second |
| IRIG | Inter-Range Instrumentation Group |
| WWVB | LF Radio WWVB Fort Collins, Colorado 60 kHz |
| DCF | LF Radio DCF77 Mainflingen, DE 77.5 kHz |
| HBG | LF Radio HBG Prangins, HB 75 kHz (ceased operation) |
| MSF | LF Radio MSF Anthorn, UK 60 kHz |
| JJY | LF Radio JJY Fukushima, JP 40 kHz, Saga, JP 60 kHz |
| LORC | MF Radio Loran-C station, 100 kHz |
| TDF | MF Radio Allouis, FR 162 kHz |
| CHU | HF Radio CHU Ottawa, Ontario |
| WWV | HF Radio WWV Fort Collins, Colorado |
| WWVH | HF Radio WWVH Kauai, Hawaii |
| NIST | NIST telephone modem |
| ACTS | NIST telephone modem |
| USNO | USNO telephone modem |
| PTB | German PTB time standard telephone modem |
| MRS | (Informal) Multi Reference Sources |
| GOOG | (Unofficial) Google Refid used by Google NTP servers as time4.google.com |
For servers on stratum 2 and below, the refid is an encoded form of the upstream time server's IP address. For IPv4, this is simply the 32-bit address; for IPv6, it would be the first 32 bits of the MD5 hash of the source address. Refids serve to detect and prevent timing loops to the first degree.[5]
The refid field is filled with status words in the case of kiss-o'-death (KoD) packets, which tell the client to stop sending requests so that the server can rest.[5] Some examples are INIT (initialization), STEP (step time change), and RATE (client requesting too fast).[33] The program output may additionally use codes not transmitted in the packet to indicate error, such as XFAC to indicate a network disconnection.[32]
The IANA maintains a registry for refid source names and KoD codes. Informal assignments can still appear.[34]
Timestamps edit
The 64-bit binary fixed-point timestamps used by NTP consist of a 32-bit part for seconds and a 32-bit part for fractional second, giving a time scale that rolls over every 232 seconds (136 years) and a theoretical resolution of 2−32 seconds (233 picoseconds). NTP uses an epoch of January 1, 1900. Therefore, the first rollover occurs on February 7, 2036.[35][36]
NTPv4 introduces a 128-bit date format: 64 bits for the second and 64 bits for the fractional-second. The most-significant 32 bits of this format is the Era Number which resolves rollover ambiguity in most cases.[37] According to Mills, "The 64-bit value for the fraction is enough to resolve the amount of time it takes a photon to pass an electron at the speed of light. The 64-bit second value is enough to provide unambiguous time representation until the universe goes dim."[38][b]
Clock synchronization algorithm edit
A typical NTP client regularly polls one or more NTP servers. The client must compute its time offset and round-trip delay. Time offset θ is positive or negative (client time > server time) difference in absolute time between the two clocks. It is defined by
- t0 is the client's timestamp of the request packet transmission,
- t1 is the server's timestamp of the request packet reception,
- t2 is the server's timestamp of the response packet transmission and
- t3 is the client's timestamp of the response packet reception.[1]: 19
To derive the expression for the offset, note that for the request packet,
The values for θ and δ are passed through filters and subjected to statistical analysis ("mitigation"). Outliers are discarded and an estimate of time offset is derived from the best three remaining candidates. The clock frequency is then adjusted to reduce the offset gradually ("discipline"), creating a feedback loop.[1]: 20
Accurate synchronization is achieved when both the incoming and outgoing routes between the client and the server have symmetrical nominal delay. If the routes do not have a common nominal delay, a systematic bias exists of half the difference between the forward and backward travel times. A number of approaches have been proposed to measure asymmetry,[39] but among practical implementations only chrony seems to have one included.[40][41]
Software implementations edit
Reference implementation edit
The NTP reference implementation, along with the protocol, has been continuously developed for over 20 years. Backwards compatibility has been maintained as new features have been added. It contains several sensitive algorithms, especially to discipline the clock, that can misbehave when synchronized to servers that use different algorithms. The software has been ported to almost every computing platform, including personal computers. It runs as a daemon called ntpd under Unix or as a service under Windows. Reference clocks are supported and their offsets are filtered and analysed in the same way as remote servers, although they are usually polled more frequently.[1]: 15–19 This implementation was audited in 2017, finding 14 potential security issues.[42]
Windows Time edit
All Microsoft Windows versions since Windows 2000 include the Windows Time service (W32Time),[43] which has the ability to synchronize the computer clock to an NTP server.
W32Time was originally implemented for the purpose of the Kerberos version 5 authentication protocol, which required time to be within 5 minutes of the correct value to prevent replay attacks. The network time server in Windows 2000 Server (and Windows XP) does not implement NTP disciplined synchronization, only locally disciplined synchronization with NTP/SNTP correction.[44]
Beginning with Windows Server 2003 and Windows Vista, the NTP provider for W32Time became compatible with a significant subset of NTPv3.[45] Microsoft states that W32Time cannot reliably maintain time synchronization with one second accuracy.[46] If higher accuracy is desired, Microsoft recommends using a newer version of Windows or different NTP implementation.[47]
Beginning with Windows 10 version 1607 and Windows Server 2016, W32Time can be configured to reach time accuracy of 1 s, 50 ms or 1 ms under certain specified operating conditions.[48][46][49]
OpenNTPD edit
In 2004, Henning Brauer of OpenBSD presented OpenNTPD, an NTPv3/SNTPv4[50] implementation with a focus on security and encompassing a privilege separated design. Whilst it is aimed more closely at the simpler generic needs of OpenBSD users, it also includes some protocol security improvements while still being compatible with existing NTP servers. The simpler code base sacrifices accuracy, deemed unnecessary in this use case.[51] A portable version is available in Linux package repositories.
NTPsec edit
NTPsec is a fork of the reference implementation that has been systematically security-hardened. The fork point was in June 2015 and was in response to a series of compromises in 2014.[52] The first production release shipped in October 2017.[53] Between removal of unsafe features, removal of support for obsolete hardware, and removal of support for obsolete Unix variants, NTPsec has been able to pare away 75% of the original codebase, making the remainder easier to audit.[54] A 2017 audit of the code showed eight security issues, including two that were not present in the original reference implementation, but NTPsec did not suffer from eight other issues that remained in the reference implementation.[55]
chrony edit
chrony is an independent NTP implementation mainly sponsored by Red Hat, who uses it as the default time program in their distributions.[56] Being written from scratch, chrony has a simpler codebase allowing for better security[57] and lower resource consumption.[58] It does not however compromise on accuracy, instead syncing faster and better than the reference ntpd in many circumstances. It is versatile enough for ordinary computers, which are unstable, go into sleep mode or have intermittent connection to the Internet. It is also designed for virtual machines, a more unstable environment.[59]
Chrony has been evaluated as "trustworthy", with only a few incidents.[60] It is able to achieve improved precision on LAN connections, using hardware timestamping on the network adapter.[40] Support for Network Time Security (NTS) was added on version 4.0.[61] chrony is available under GNU General Public License version 2, was created by Richard Curnow in 1997 and is currently maintained by Miroslav Lichvar.[58]
Others edit
- Ntimed was started by Poul-Henning Kamp of FreeBSD in 2014 and abandoned in 2015.[62] The implementation was sponsored by the Linux Foundation.[63]
- systemd-timesyncd is the SNTP client built into systemd. It is used by Debian since version "bookworm"[64] and the downstream Ubuntu.
Leap seconds edit
On the day of a leap second event, ntpd receives notification from either a configuration file, an attached reference clock, or a remote server. Although the NTP clock is actually halted during the event, because of the requirement that time must appear to be strictly increasing, any processes that query the system time cause it to increase by a tiny amount, preserving the order of events. If a negative leap second should ever become necessary, it would be deleted with the sequence 23:59:58, 00:00:00, skipping 23:59:59.[65]
An alternative implementation, called leap smearing, consists in introducing the leap second incrementally during a period of 24 hours, from noon to noon in UTC time. This implementation is used by Google (both internally and on their public NTP servers), Amazon AWS,[66] and Facebook.[67] Chrony supports leap smear in smoothtime and leapsecmode configurations, but such use is not to be mixed with a public NTP pool as leap smear is non-standard and will throw off client calculation in a mix.[68]
Security concerns edit
Because adjusting system time is generally a privileged operation, part or all of NTP code has to be run with some privileges in order to support its core functionality. Only a few other security problems have been identified in the reference implementation of the NTP codebase, but those that appeared in 2009[which?] were cause for significant concern.[69][70] The protocol has been undergoing revision and review throughout its history. The codebase for the reference implementation has undergone security audits from several sources for several years.[71]
A stack buffer overflow exploit was discovered and patched in 2014.[72] Apple was concerned enough about this vulnerability that it used its auto-update capability for the first time.[73] On systems using the reference implementation, which is running with root user's credential, this could allow unlimited access. Some other implementations, such as OpenNTPD, have smaller code base and adopted other mitigation measures like privilege separation, are not subject to this flaw.[74]
A 2017 security audit of three NTP implementations, conducted on behalf of the Linux Foundation's Core Infrastructure Initiative, suggested that both NTP[75][76] and NTPsec[77] were more problematic than Chrony[78] from a security standpoint.[79]
NTP servers can be susceptible to man-in-the-middle attacks unless packets are cryptographically signed for authentication.[80] The computational overhead involved can make this impractical on busy servers, particularly during denial of service attacks.[81] NTP message spoofing from a man-in-the-middle attack can be used to alter clocks on client computers and allow a number of attacks based on bypassing of cryptographic key expiration.[82] Some of the services affected by fake NTP messages identified are TLS, DNSSEC, various caching schemes (such as DNS cache), Border Gateway Protocol (BGP), Bitcoin [citation needed]and a number of persistent login schemes.[83][84]
NTP has been used in distributed denial of service attacks.[85][86] A small query is sent to an NTP server with the return IP address spoofed to be the target address. Similar to the DNS amplification attack, the server responds with a much larger reply that allows an attacker to substantially increase the amount of data being sent to the target. To avoid participating in an attack, NTP server software can be upgraded or servers can be configured to ignore external queries.[87]
Secure extensions edit
NTP itself includes support for authenticating servers to clients. NTPv3 supports a symmetric key mode, which is not useful against MITM. The public key system known as "autokey" in NTPv4 adapted from IPSec offers useful authentication,[80] but is not practical for a busy server.[81] Autokey was also later found to suffer from several design flaws,[88] with no correction published, save for a change in the message authentication code.[16]
Network Time Security (NTS) is a secure version of NTPv4 with TLS and AEAD.[89] The main improvement over previous attempts is that a separate "key establishment" server handles the heavy asymmetric cryptography, which needs to be done only once. If the server goes down, previous users would still be able to fetch time without fear of MITM.[90] NTS is currently supported by several time servers,[91][92] including Cloudflare. It is supported by NTPSec and chrony.[93]
Microsoft also has an approach to authenticate NTPv3/SNTPv4 packets using a Windows domain identity, known as MS-SNTP.[94] This system is implemented in the reference ntpd and chrony, using samba for the domain connection. [95]
See also edit
Notes edit
- ^ Telecommunication systems use a different definition for clock strata.
- ^ 2−64 seconds is about 54 zeptoseconds (light would travel 16.26 picometers, or approximately 0.31 × Bohr radius), and 264 seconds is about 585 billion years.
References edit
- ^ a b c d e f David L. Mills (12 December 2010). Computer Network Time Synchronization: The Network Time Protocol. Taylor & Francis. pp. 12–. ISBN 978-0-8493-5805-0. Archived from the original on 18 July 2014. Retrieved 16 October 2016.
- ^ a b c "Executive Summary: Computer Network Time Synchronization". Archived from the original on 2011-11-02. Retrieved 2011-11-21.
- ^ a b c d "NTP FAQ". The NTP Project. Archived from the original on 2011-09-06. Retrieved 2011-08-27.
- ^ "Port Numbers". The Internet Assigned Numbers Authority (IANA). Archived from the original on 2001-06-04. Retrieved 2011-01-19.
- ^ a b c d e f g D. Mills; J. Burbank; W. Kasch (August 2010). J. Martin (ed.). Network Time Protocol Version 4: Protocol and Algorithms Specification. Internet Engineering Task Force (IETF). doi:10.17487/RFC5905. ISSN 2070-1721. RFC 5905. Proposed Standard. Obsoletes RFC 1305, 4330. Updated by RFC 7822, 8573 and 9109.
- ^ a b David L. Mills (March 1992). Network Time Protocol (Version 3) - Specification, Implementation and Analysis. Network Working Group. doi:10.17487/RFC1305. RFC 1305. Obsolete. Obsoleted by RFC 5905. Obsoletes RFC 958, 1059 and 1119.
- ^ D. Mills (September 1985). Network Time Protocol (NTP). Network Working Group. doi:10.17487/RFC0958. RFC 958. Obsolete. Obsoleted by RFC 1059, 1119 and 1305.
- ^ D. Mills (July 1988). Network Time Protocol (Version 1) Specification and Implementation. Network Working Group. doi:10.17487/RFC1059. RFC 1059. Obsolete. Obsoleted by RFC 1119 and 1305.
- ^ D. Mills (September 1989). Network Time Protocol (Version 2) Specification and Implementation. Network Working Group. doi:10.17487/RFC1119. RFC 1119. Obsolete. Obsoleted by RFC 1305. Obsoletes RFC 958 and 1059.
- ^ a b D. Mills (August 1992). Type of Service in the Internet Protocol Suite. Network Working Group. doi:10.17487/RFC1361. RFC 1361. Obsolete. Obsoleted by RFC 1769.
- ^ D. Mills (March 1995). Simple Network Time Protocol (SNTP). Network Working Group. doi:10.17487/RFC1769. RFC 1769. Obsolete. Obsoleted by RFC 2030. Obsoletes RFC 1361.
- ^ a b D. Mills (October 1996). Simple Network Time Protocol (SNTP) Version 4 for IPv4, IPv6 and OSI. Network Working Group. doi:10.17487/RFC2030. RFC 2030. Obsolete. Obsoleted by RFC 4330. Obsoletes RFC 1769.
- ^ a b D. Mills (January 2006). Simple Network Time Protocol (SNTP) Version 4 for IPv4, IPv6 and OSI. Network Working Group. doi:10.17487/RFC4330. RFC 4330. Obsolete. Obsoletes RFC 2030 and 1769. Obsoleted by RFC 5905.
- ^ D.L. Mills (April 1981). DCNET Internet Clock Service. IETF. doi:10.17487/RFC0778. RFC 778. Historic.
- ^ T. Mizrahi; D. Mayer (March 2016). Network Time Protocol Version 4 (NTPv4) Extension Fields. IETF. doi:10.17487/RFC7822. ISSN 2070-1721. RFC 7822. Informational. Updates RFC 5905.
- ^ a b A. Malhotra; S. Goldberg (June 2019). Message Authentication Code for the Network Time Protocol. Internet Engineering Task Force. doi:10.17487/RFC8573. ISSN 2070-1721. RFC 8573. Proposed Standard. Updates RFC 5905.
- ^ F. Gont; G. Gont; M. Lichvar (August 2021). Network Time Protocol Version 4: Port Randomization. Internet Engineering Task Force. doi:10.17487/RFC9109. ISSN 2070-1721. RFC 9109. Proposed Standard. Updates RFC 5905.
- ^ D.L. Mills (25 February 1981), Time Synchronization in DCNET Hosts, archived from the original on 1996-12-30
- ^ "TIMED(8)", UNIX System Manager's Manual, archived from the original on 2011-07-22, retrieved 2017-09-12
- ^ David L. Mills (October 1991). "Internet Time Synchronization: The Network Time Protocol" (PDF). IEEE Transactions on Communications. 39 (10): 1482–1493. doi:10.1109/26.103043. Archived (PDF) from the original on 2016-06-10. Retrieved 2017-11-06.
- ^ David L. Mills (March 1992). Network Time Protocol (Version 3) - Specification, Implementation and Analysis. Network Working Group. doi:10.17487/RFC1305. RFC 1305. Obsolete.
The clock-selection procedure was modified to remove the first of the two sorting/discarding steps and replace with an algorithm first proposed by Marzullo and later incorporated in the Digital Time Service. These changes do not significantly affect the ordinary operation of or compatibility with various versions of NTP, but they do provide the basis for formal statements of correctness.
- ^ David L. Mills (15 November 2010). Computer Network Time Synchronization: The Network Time Protocol on Earth and in Space, Second Edition. CRC Press. p. 377. ISBN 978-1-4398-1464-2.
- ^ a b c "Future Plans", Network Time Synchronization Research Project, archived from the original on 23 December 2014, retrieved 24 December 2014
- ^ "NTP Needs Money: Is A Foundation The Answer?". InformationWeek. March 23, 2015. Archived from the original on April 10, 2015. Retrieved April 4, 2015.
- ^ "NTP's Fate Hinges On 'Father Time'". InformationWeek. March 11, 2015. Archived from the original on April 10, 2015. Retrieved April 4, 2015.
- ^ a b "Network Time Protocols (ntp): Documents". datatracker.ietf.org. Retrieved 27 December 2022.
- ^ Lichvar, Miroslav (6 December 2022). "Network Time Protocol Version 5". www.ietf.org.
- ^ D. Mills; J. Burbank; W. Kasch (August 2010). J. Martin (ed.). Network Time Protocol Version 4: Protocol and Algorithms Specification. Internet Engineering Task Force (IETF). doi:10.17487/RFC5905. ISSN 2070-1721. RFC 5905. Proposed Standard.
Primary servers and clients complying with a subset of NTP, called the Simple Network Time Protocol (SNTPv4) [...], do not need to implement the mitigation algorithms [...] The fully developed NTPv4 implementation is intended for [...] servers with multiple upstream servers and multiple downstream servers [...] Other than these considerations, NTP and SNTP servers and clients are completely interoperable and can be intermixed [...]
- ^ "Combining PTP with NTP to Get the Best of Both Worlds". www.redhat.com.
Programs from the linuxptp package can be used in a combination with an NTP daemon. A PTP clock on a NIC is synchronized by ptp4l and is used as a reference clock by chronyd or ntpd for synchronization of the system clock.
- ^ RFC 5905, p. 21
- ^ "Network Time Protocol: Best Practices White Paper". Archived from the original on 1 October 2013. Retrieved 15 October 2013.
- ^ a b "'ntpq -p' output". NLUG.ML1.co.uk. Archived from the original on 2018-11-12. Retrieved 2018-11-12.
- ^ "Event Messages and Status Words". docs.ntpsec.org.
Refid codes are used in kiss-o'-death (KoD) packets, the reference identifier field in ntpq and ntpmon billboard displays and log messages.
- ^ "Network Time Protocol (NTP) Parameters". www.iana.org.
- ^ David L. Mills (12 May 2012). "The NTP Era and Era Numbering". Archived from the original on 26 October 2016. Retrieved 24 September 2016.
- ^ W. Richard Stevens; Bill Fenner; Andrew M. Rudoff (2004). UNIX Network Programming. Addison-Wesley Professional. pp. 582–. ISBN 978-0-13-141155-5. Archived from the original on 2019-03-30. Retrieved 2016-10-16.
- ^ "A look at the Year 2036/2038 problems and time proofness in various systems". 14 March 2017. Archived from the original on 2018-07-21. Retrieved 2018-07-20.
- ^ University of Delaware Digital Systems Seminar presentation by David Mills, 2006-04-26
- ^ Gotoh, T.; Imamura, K.; Kaneko, A. (2002). "Improvement of NTP time offset under the asymmetric network with double packets method". Conference Digest Conference on Precision Electromagnetic Measurements. Conference on Precision Electromagnetic Measurements. pp. 448–449. doi:10.1109/CPEM.2002.1034915. ISBN 0-7803-7242-5.
- ^ a b Lichvar, Miroslav (18 September 2018). "chrony – chrony.conf(5)". Chrony project. Retrieved 2 August 2020.
This directive enables hardware timestamping of NTP packets sent to and received from the specified network interface.
- ^ "sourcestats.c, function estimate_asymmetry()". git.tuxfamily.org (chrony).
- ^ "Pentest-Report NTP 01.2017" (PDF). Cure53. 2017. Archived (PDF) from the original on 2018-12-01. Retrieved 2019-07-03.
- ^ "Windows Time Service Technical Reference". technet.microsoft.com. 2011-08-17. Archived from the original on 2011-09-06. Retrieved 2011-09-19.
- ^ "Windows Time Service page at NTP.org". Support.NTP.org. 2008-02-25. Archived from the original on 2017-05-14. Retrieved 2017-05-01.
- ^ "How the Windows Time Service Works". technet.microsoft.com. 2010-03-12. Archived from the original on 2011-09-24. Retrieved 2011-09-19.
- ^ a b "Support boundary to configure the Windows Time service for high accuracy environments". Microsoft. 2011-10-19. Archived from the original on 2009-01-12. Retrieved 2008-12-10.
- ^ Ned Pyle (2007-10-23). "High Accuracy W32time Requirements". Microsoft. Archived from the original on 2012-10-17. Retrieved 2012-08-26.
- ^ "Windows Server 2016 Accurate Time". technet.microsoft.com. Archived from the original on 2016-12-02. Retrieved 2016-12-07.
- ^ dahavey. "Support boundary for high-accuracy time". docs.microsoft.com. Retrieved 2021-07-24.
- ^ "ntpd(8) - OpenBSD manual pages". man.openbsd.org.
It implements the Simple Network Time Protocol version 4, as described in RFC 5905, and the Network Time Protocol version 3, as described in RFC 1305.
- ^ The OpenBSD Project (21 August 2006). "FAQ 6.12.1: 'But OpenNTPD isn't as accurate as the ntp.org daemon!'". The OpenBSD Project. Archived from the original on 2016-02-05. Retrieved 2020-05-14.
- ^ Raymond, Eric S. (2017-03-30). "NTPsec: a Secure, Hardened NTP Implementation | Linux Journal". Linux Journal. Archived from the original on 2024-01-26. Retrieved 2024-01-26.
- ^ "The Secure Network Time Protocol (NTPsec) Distribution". Archived from the original on 2019-01-13. Retrieved 2019-01-12.
- ^ Liska, Allan (December 10, 2016). NTP Security: A Quick-Start Guide. Apress. pp. 80–. ISBN 978-1-4842-2412-0.
- ^ "Pentest-Report NTPsec 01.2017" (PDF). Cure53. 2017. Archived (PDF) from the original on 2019-07-04. Retrieved 2019-07-03.
- ^ Lichvar, Miroslav (20 July 2016). "Combining PTP with NTP to Get the Best of Both Worlds". Red Hat Enterprise Linux Blog. Red Hat. Archived from the original on 30 July 2016. Retrieved 19 November 2017.
Starting with Red Hat Enterprise Linux 7.0 (and now in Red Hat Enterprise Linux 6.8) a more versatile NTP implementation is also provided via the chrony package
- ^ "Securing Network Time". Core Infrastructure Initiative, a Linux Foundation Collaborative Project. Core Infrastructure Initiative. 27 September 2017. Archived from the original on 28 October 2017. Retrieved 19 November 2017.
In sum, the Chrony NTP software stands solid and can be seen as trustworthy
- ^ a b "chrony introduction". TuxFamily, a non-profit organization. chrony. Archived from the original on 9 December 2009. Retrieved 19 November 2017.
The software is supported on Linux, FreeBSD, NetBSD, macOS, and Solaris.
- ^ Both, David. "Manage NTP with Chrony". Opensource.com. Archived from the original on 29 June 2019. Retrieved 29 June 2019.
- ^ Heiderich, Mario (August 2017). "Pentest-Report Chrony 08.2017" (PDF). Cure53.de Team. wiki.mozilla.org, AKA MozillaWiki or WikiMO. Archived from the original (PDF) on 5 October 2017. Retrieved 19 November 2017.
Withstanding eleven full days of on-remote testing in August of 2017 means that Chrony is robust, strong, and developed with security in mind.
- ^ "chrony/chrony.git - Official Git repository for the Chrony project". git.tuxfamily.org. Retrieved 2021-07-31.
- ^ Poul-Henning, Kamp. "20140926 – Playing with time again". PHK's Bikeshed. Archived from the original on 20 December 2019. Retrieved 4 June 2015.
- ^ Poul-Henning, Kamp. "Network time synchronization software, NTPD replacement". ntimed git repository README file. Github. Archived from the original on 2 August 2015. Retrieved 4 June 2015.
- ^ "Switching from OpenNTPd to Chrony - anarcat". anarc.at.
So in effect, systemd-timesyncd became the default NTP daemon in Debian in bookworm, which I find somewhat surprising.
- ^ David Mills. "The NTP Timescale and Leap Seconds". Archived from the original on 7 September 2013. Retrieved 15 October 2013.
- ^ "Google Developers Leap Smear". Archived from the original on 4 April 2019. Retrieved 4 April 2019.
- ^ Obleukhov, Oleg (18 March 2020). "Building a more accurate time service at Facebook scale". Engineering at Meta.
- ^ "chrony – Frequently Asked Questions". chrony.tuxfamily.org.
- ^ "Security Notice". Support.NTP.org. 2009-12-10. Retrieved 2011-01-12.[permanent dead link]
- ^ "Cisco IOS Software Network Time Protocol Packet Vulnerability". Cisco Systems. 23 September 2009. Archived from the original on 11 June 2020. Retrieved 11 June 2020.
- ^ "Code Audit". Support.NTP.org. 2009-06-13. Retrieved 2011-01-12.
- ^ "Network Time Protocol Vulnerabilities (Update C) | ICS-CERT". Ics-cert.us-cert.gov. Archived from the original on 2014-12-20. Retrieved 2015-04-15.
- ^ Cunningham, Andrew (Dec 23, 2014). "Apple automatically patches Macs to fix severe NTP security flaw". arstechnica. Archived from the original on April 15, 2015. Retrieved Apr 29, 2015.
- ^ Fairhead, Harry (23 December 2014). "NTP The Latest Open Source Security Problem". I Programmer. Archived from the original on 24 December 2014. Retrieved 24 December 2014.
- ^ NTP SecurityNotice Page Archived 2014-02-19 at the Wayback Machine
- ^ NVD NIST Product Search NTP
- ^ NVD NIST Product Search NTPsec Archived 2020-06-26 at the Wayback Machine
- ^ NVD NIST Product Search Chrony Archived 2020-06-26 at the Wayback Machine
- ^ "CII Audit Identifies Most Secure NTP Implementation". The Linux Foundation. September 28, 2017. Archived from the original on 2018-02-03. Retrieved 2019-07-03.
- ^ a b Network Time Protocol Version 4: Autokey Specification. IETF. June 2010. doi:10.17487/RFC5906. RFC 5906.
- ^ a b "NTP Security Analysis". Archived from the original on 7 September 2013. Retrieved 11 October 2013.
- ^ Jose Selvi (2014-10-16). "Bypassing HTTP Strict Transport Security" (PDF). Archived from the original (PDF) on 2014-10-18. Retrieved 2014-10-16.
- ^ Aanchal Malhotra; Isaac E. Cohen; Erik Brakke & Sharon Goldberg (20 October 2015). "Attacking the Network Time Protocol" (PDF). NDSS. Archived from the original (PDF) on 22 October 2015. Retrieved 27 October 2015.
- ^ "Attacking the Network Time Protocol". www.cs.bu.edu. Archived from the original on 2015-10-24. Retrieved 2015-10-27.
- ^ Goodin, Dan (2014-01-13). "New DoS attacks taking down game sites deliver crippling 100Gbps floods". Ars Technica. Archived from the original on 2014-01-24. Retrieved 2014-01-25.
- ^ Lee, Dave (2014-02-11). "Huge Hack 'Ugly Sign of Future' for Internet Threats". BBC. Archived from the original on 2014-02-11. Retrieved 2014-02-12.
- ^ "DRDoS / Amplification Attack using ntpdc monlist command". support.NTP.org. 2010-04-24. Archived from the original on 2014-03-30. Retrieved 2014-04-13.
- ^ Dieter Sibold; Stephen Röttger (2012). Analysis of NTP’s Autokey Protocol (PDF). IETF 83.
- ^ "nts.time.nl homepage". nts.time.nl. Retrieved 2021-08-19.
- ^ D. Franke; D. Sibold; K. Teichel; M. Dansarie; R. Sundblad (September 2020). Network Time Security for the Network Time Protocol. Internet Engineering Task Force. doi:10.17487/RFC8915. ISSN 2070-1721. RFC 8915. Proposed Standard.
- ^ Langer, Martin (2019-12-05). "Setting up NTS-Secured NTP with NTPsec". Weberblog.net. Retrieved 2021-08-19.
- ^ "How to use NTS | Netnod". Netnod. Retrieved 2021-08-19.
- ^ "Network Time Security · Cloudflare Time Services docs". developers.cloudflare.com. 5 February 2024.
- ^ "[MS-SNTP]: Network Time Protocol (NTP) Authentication Extensions". 24 June 2021.
- ^ "Comparison of NTP implementations". chrony.tuxfamily.org. Retrieved 2019-10-08.
Further reading edit
External links edit
- Official website
- Official Stratum One Time Servers list
- IETF NTP working group
- Microsft Windows accurate time guide and more
- Time and NTP paper
- NTP Survey 2005
- Current NIST leap seconds file compatible with ntpd
- David L. Mills, A Brief History of NTP Time: Confessions of an Internet Timekeeper (PDF), retrieved 2021-02-07