In computing, BIOS (/ˈbaɪɒs, -oʊs/, BY-oss, -ohss; Basic Input/Output System, also known as the System BIOS, ROM BIOS, BIOS ROM or PC BIOS) is firmware used to provide runtime services for operating systems and programs and to perform hardware initialization during the booting process (power-on startup).[1] The BIOS firmware comes pre-installed on an IBM PC or IBM PC compatible's system board and exists in some UEFI-based systems to maintain compatibility with operating systems that do not support UEFI native operation.[2][3] The name originates from the Basic Input/Output System used in the CP/M operating system in 1975.[4][5] The BIOS originally proprietary to the IBM PC has been reverse engineered by some companies (such as Phoenix Technologies) looking to create compatible systems. The interface of that original system serves as a de facto standard.
 | |
| Year started | 1981[a] |
|---|---|
| Organization | Originally IBM as proprietary software, later industry wide as a de facto standard. In 1996, the BIOS Boot Specification was written by Compaq, Phoenix Technologies and Intel. |
| Successor | UEFI |
The BIOS in older PCs initializes and tests the system hardware components (power-on self-test or POST for short), and loads a boot loader from a mass storage device which then initializes a kernel. In the era of DOS, the BIOS provided BIOS interrupt calls for the keyboard, display, storage, and other input/output (I/O) devices that standardized an interface to application programs and the operating system. More recent operating systems do not use the BIOS interrupt calls after startup.[6]
Most BIOS implementations are specifically designed to work with a particular computer or motherboard model, by interfacing with various devices especially system chipset. Originally, BIOS firmware was stored in a ROM chip on the PC motherboard. In later computer systems, the BIOS contents are stored on flash memory so it can be rewritten without removing the chip from the motherboard. This allows easy, end-user updates to the BIOS firmware so new features can be added or bugs can be fixed, but it also creates a possibility for the computer to become infected with BIOS rootkits. Furthermore, a BIOS upgrade that fails could brick the motherboard.
The last version of Microsoft Windows to officially support running on PCs which use legacy BIOS firmware is Windows 10 as Windows 11 requires a UEFI-compliant system (except for IoT Enterprise editions of Windows 11 since version 24H2[7]).
Unified Extensible Firmware Interface (UEFI) is a successor to the legacy PC BIOS, aiming to address its technical limitations.[8] Since 2020, all PCs for Intel platforms no longer support Legacy BIOS.[9]
History
edit/* C P / M B A S I C I / O S Y S T E M (B I O S) COPYRIGHT (C) GARY A. KILDALL JUNE, 1975 */ […] /* B A S I C D I S K O P E R A T I N G S Y S T E M (B D O S) COPYRIGHT (C) GARY A. KILDALL JUNE, 1975 */— An excerpt from the BDOS.PLM file header in the PL/M source code of CP/M 1.1 or 1.2 for Lawrence Livermore Laboratories (LLL)[4]
The term BIOS (Basic Input/Output System) was created by Gary Kildall[10][11] and first appeared in the CP/M operating system in 1975,[4][5][11][12][13][14] describing the machine-specific part of CP/M loaded during boot time that interfaces directly with the hardware.[5] (A CP/M machine usually has only a simple boot loader in its ROM.)
Versions of MS-DOS, PC DOS or DR-DOS contain a file called variously "IO.SYS", "IBMBIO.COM", "IBMBIO.SYS", or "DRBIOS.SYS"; this file is known as the "DOS BIOS" (also known as the "DOS I/O System") and contains the lower-level hardware-specific part of the operating system. Together with the underlying hardware-specific but operating system-independent "System BIOS", which resides in ROM, it represents the analogue to the "CP/M BIOS".
The BIOS originally proprietary to the IBM PC has been reverse engineered by some companies (such as Phoenix Technologies) looking to create compatible systems.
With the introduction of PS/2 machines, IBM divided the System BIOS into real- and protected-mode portions. The real-mode portion was meant to provide backward compatibility with existing operating systems such as DOS, and therefore was named "CBIOS" (for "Compatibility BIOS"), whereas the "ABIOS" (for "Advanced BIOS") provided new interfaces specifically suited for multitasking operating systems such as OS/2.[15]
User interface
editThe BIOS of the original IBM PC and XT had no interactive user interface. Error codes or messages were displayed on the screen, or coded series of sounds were generated to signal errors when the power-on self-test (POST) had not proceeded to the point of successfully initializing a video display adapter. Options on the IBM PC and XT were set by switches and jumpers on the main board and on expansion cards. Starting around the mid-1990s, it became typical for the BIOS ROM to include a "BIOS configuration utility" (BCU[16]) or "BIOS setup utility", accessed at system power-up by a particular key sequence. This program allowed the user to set system configuration options, of the type formerly set using DIP switches, through an interactive menu system controlled through the keyboard. In the interim period, IBM-compatible PCs—including the IBM AT—held configuration settings in battery-backed RAM and used a bootable configuration program on floppy disk, not in the ROM, to set the configuration options contained in this memory. The floppy disk was supplied with the computer, and if it was lost the system settings could not be changed. The same applied in general to computers with an EISA bus, for which the configuration program was called an EISA Configuration Utility (ECU).
A modern Wintel-compatible computer provides a setup routine essentially unchanged in nature from the ROM-resident BIOS setup utilities of the late 1990s; the user can configure hardware options using the keyboard and video display. The modern Wintel machine may store the BIOS configuration settings in flash ROM, perhaps the same flash ROM that holds the BIOS itself.
Operation
editSystem startup
editEarly Intel processors started at physical address 000FFFF0h. Systems with later processors provide logic to start running the BIOS from the system ROM. [17]
If the system has just been powered up or the reset button was pressed ("cold boot"), the full power-on self-test (POST) is run. If Ctrl+Alt+Delete was pressed ("warm boot"), a special flag value stored in nonvolatile BIOS memory ("CMOS") tested by the BIOS allows bypass of the lengthy POST and memory detection.
The POST identifies, tests and initializes system devices such as the CPU, chipset, RAM, motherboard, video card, keyboard, mouse, hard disk drive, optical disc drive and other hardware, including integrated peripherals.
Early IBM PCs had a routine in the POST that would download a program into RAM through the keyboard port and run it.[18][19] This feature was intended for factory test or diagnostic purposes.
Boot process
editAfter the option ROM scan is completed and all detected ROM modules with valid checksums have been called, or immediately after POST in a BIOS version that does not scan for option ROMs, the BIOS calls INT 19h to start boot processing. Post-boot, programs loaded can also call INT 19h to reboot the system, but they must be careful to disable interrupts and other asynchronous hardware processes that may interfere with the BIOS rebooting process, or else the system may hang or crash while it is rebooting.
When INT 19h is called, the BIOS attempts to locate boot loader software on a "boot device", such as a hard disk, a floppy disk, CD, or DVD. It loads and executes the first boot software it finds, giving it control of the PC.[20]
The BIOS uses the boot devices set in Nonvolatile BIOS memory (CMOS), or, in the earliest PCs, DIP switches. The BIOS checks each device in order to see if it is bootable by attempting to load the first sector (boot sector). If the sector cannot be read, the BIOS proceeds to the next device. If the sector is read successfully, some BIOSes will also check for the boot sector signature 0x55 0xAA in the last two bytes of the sector (which is 512 bytes long), before accepting a boot sector and considering the device bootable.[b]
When a bootable device is found, the BIOS transfers control to the loaded sector. The BIOS does not interpret the contents of the boot sector other than to possibly check for the boot sector signature in the last two bytes. Interpretation of data structures like partition tables and BIOS Parameter Blocks is done by the boot program in the boot sector itself or by other programs loaded through the boot process.
A non-disk device such as a network adapter attempts booting by a procedure that is defined by its option ROM or the equivalent integrated into the motherboard BIOS ROM. As such, option ROMs may also influence or supplant the boot process defined by the motherboard BIOS ROM.
With the El Torito optical media boot standard, the optical drive actually emulates a 3.5" high-density floppy disk to the BIOS for boot purposes. Reading the "first sector" of a CD-ROM or DVD-ROM is not a simply defined operation like it is on a floppy disk or a hard disk. Furthermore, the complexity of the medium makes it difficult to write a useful boot program in one sector. The bootable virtual floppy disk can contain software that provides access to the optical medium in its native format.
Boot priority
editThe user can select the boot priority implemented by the BIOS. For example, most computers have a hard disk that is bootable, but sometimes there is a removable-media drive that has higher boot priority, so the user can cause a removable disk to be booted.
In most modern BIOSes, the boot priority order can be configured by the user. In older BIOSes, limited boot priority options are selectable; in the earliest BIOSes, a fixed priority scheme was implemented, with floppy disk drives first, fixed disks (i.e., hard disks) second, and typically no other boot devices supported, subject to modification of these rules by installed option ROMs. The BIOS in an early PC also usually would only boot from the first floppy disk drive or the first hard disk drive, even if there were two drives installed.
Boot failure
editOn the original IBM PC and XT, if no bootable disk was found, the BIOS would try to start ROM BASIC with the interrupt call INT 18h. Since few programs used BASIC in ROM, clone PC makers left it out; then a computer that failed to boot from a disk would display "No ROM BASIC" and halt (in response to INT 18h).
Later computers would display a message like "No bootable disk found"; some would prompt for a disk to be inserted and a key to be pressed to retry the boot process. A modern BIOS may display nothing or may automatically enter the BIOS configuration utility when the boot process fails.
Boot environment
editThe environment for the boot program is very simple: the CPU is in real mode and the general-purpose and segment registers are undefined, except SS, SP, CS, and DL. CS:IP always points to physical address 0x07C00. What values CS and IP actually have is not well defined. Some BIOSes use a CS:IP of 0x0000:0x7C00 while others may use 0x07C0:0x0000.[21] Because boot programs are always loaded at this fixed address, there is no need for a boot program to be relocatable. DL may contain the drive number, as used with INT 13h, of the boot device. SS:SP points to a valid stack that is presumably large enough to support hardware interrupts, but otherwise SS and SP are undefined. (A stack must be already set up in order for interrupts to be serviced, and interrupts must be enabled in order for the system timer-tick interrupt, which BIOS always uses at least to maintain the time-of-day count and which it initializes during POST, to be active and for the keyboard to work. The keyboard works even if the BIOS keyboard service is not called; keystrokes are received and placed in the 15-character type-ahead buffer maintained by BIOS.) The boot program must set up its own stack, because the size of the stack set up by BIOS is unknown and its location is likewise variable; although the boot program can investigate the default stack by examining SS:SP, it is easier and shorter to just unconditionally set up a new stack.[22]
At boot time, all BIOS services are available, and the memory below address 0x00400 contains the interrupt vector table. BIOS POST has initialized the system timers, interrupt controller(s), DMA controller(s), and other motherboard/chipset hardware as necessary to bring all BIOS services to ready status. DRAM refresh for all system DRAM in conventional memory and extended memory, but not necessarily expanded memory, has been set up and is running. The interrupt vectors corresponding to the BIOS interrupts have been set to point at the appropriate entry points in the BIOS, hardware interrupt vectors for devices initialized by the BIOS have been set to point to the BIOS-provided ISRs, and some other interrupts, including ones that BIOS generates for programs to hook, have been set to a default dummy ISR that immediately returns. The BIOS maintains a reserved block of system RAM at addresses 0x00400–0x004FF with various parameters initialized during the POST. All memory at and above address 0x00500 can be used by the boot program; it may even overwrite itself.[23][24]
Extensions (option ROMs)
editPeripheral cards such as hard disk drive host bus adapters and video cards have their own firmware, and BIOS extension option ROM may be a part of the expansion card firmware, which provide additional functionality to BIOS. Code in option ROMs runs before the BIOS boots the operating system from mass storage. These ROMs typically test and initialize hardware, add new BIOS services, or replace existing BIOS services with their own services. For example, a SCSI controller usually has a BIOS extension ROM that adds support for hard drives connected through that controller. An extension ROM could in principle contain operating system, or it could implement an entirely different boot process such as network booting. Operation of an IBM-compatible computer system can be completely changed by removing or inserting an adapter card (or a ROM chip) that contains a BIOS extension ROM.
The motherboard BIOS typically contains code for initializing and bootstrapping integrated display and integrated storage. In addition, plug-in adapter cards such as SCSI, RAID, network interface cards, and video cards often include their own BIOS (e.g. Video BIOS), complementing or replacing the system BIOS code for the given component. Even devices built into the motherboard can behave in this way; their option ROMs can be a part of the motherboard BIOS.
An add-in card requires an option ROM if the card is not supported by the motherboard BIOS and the card needs to be initialized or made accessible through BIOS services before the operating system can be loaded (usually this means it is required in the boot process). An additional advantage of ROM on some early PC systems (notably including the IBM PCjr) was that ROM was faster than main system RAM. (On modern systems, the case is very much the reverse of this, and BIOS ROM code is usually copied ("shadowed") into RAM so it will run faster.)
Boot procedure
editIf an expansion ROM wishes to change the way the system boots (such as from a network device or a SCSI adapter) in a cooperative way, it can use the BIOS Boot Specification (BBS) API to register its ability to do so. Once the expansion ROMs have registered using the BBS APIs, the user can select among the available boot options from within the BIOS's user interface. This is why most BBS compliant PC BIOS implementations will not allow the user to enter the BIOS's user interface until the expansion ROMs have finished executing and registering themselves with the BBS API.[citation needed]
Also, if an expansion ROM wishes to change the way the system boots unilaterally, it can simply hook INT 19h or other interrupts normally called from interrupt 19h, such as INT 13h, the BIOS disk service, to intercept the BIOS boot process. Then it can replace the BIOS boot process with one of its own, or it can merely modify the boot sequence by inserting its own boot actions into it, by preventing the BIOS from detecting certain devices as bootable, or both. Before the BIOS Boot Specification was promulgated, this was the only way for expansion ROMs to implement boot capability for devices not supported for booting by the native BIOS of the motherboard.[citation needed]
Initialization
editAfter the motherboard BIOS completes its POST, most BIOS versions search for option ROM modules, also called BIOS extension ROMs, and execute them. The motherboard BIOS scans for extension ROMs in a portion of the "upper memory area" (the part of the x86 real-mode address space at and above address 0xA0000) and runs each ROM found, in order. To discover memory-mapped option ROMs, a BIOS implementation scans the real-mode address space from 0x0C0000 to 0x0F0000 on 2 KB (2,048 bytes) boundaries, looking for a two-byte ROM signature: 0x55 followed by 0xAA. In a valid expansion ROM, this signature is followed by a single byte indicating the number of 512-byte blocks the expansion ROM occupies in real memory, and the next byte is the option ROM's entry point (also known as its "entry offset"). If the ROM has a valid checksum, the BIOS transfers control to the entry address, which in a normal BIOS extension ROM should be the beginning of the extension's initialization routine.
At this point, the extension ROM code takes over, typically testing and initializing the hardware it controls and registering interrupt vectors for use by post-boot applications. It may use BIOS services (including those provided by previously initialized option ROMs) to provide a user configuration interface, to display diagnostic information, or to do anything else that it requires. It is possible that an option ROM will not return to BIOS, pre-empting the BIOS's boot sequence altogether.
An option ROM should normally return to the BIOS after completing its initialization process. Once (and if) an option ROM returns, the BIOS continues searching for more option ROMs, calling each as it is found, until the entire option ROM area in the memory space has been scanned.
Physical placement
editOption ROMs normally reside on adapter cards. However, the original PC, and perhaps also the PC XT, have a spare ROM socket on the motherboard (the "system board" in IBM's terms) into which an option ROM can be inserted, and the four ROMs that contain the BASIC interpreter can also be removed and replaced with custom ROMs which can be option ROMs. The IBM PCjr is unique among PCs in having two ROM cartridge slots on the front. Cartridges in these slots map into the same region of the upper memory area used for option ROMs, and the cartridges can contain option ROM modules that the BIOS would recognize. The cartridges can also contain other types of ROM modules, such as BASIC programs, that are handled differently. One PCjr cartridge can contain several ROM modules of different types, possibly stored together in one ROM chip.
Operating system services
editThe BIOS ROM is customized to the particular manufacturer's hardware, allowing low-level services (such as reading a keystroke or writing a sector of data to diskette) to be provided in a standardized way to programs, including operating systems. For example, an IBM PC might have either a monochrome or a color display adapter (using different display memory addresses and hardware), but a single, standard, BIOS system call may be invoked to display a character at a specified position on the screen in text mode or graphics mode.
The BIOS provides a small library of basic input/output functions to operate peripherals (such as the keyboard, rudimentary text and graphics display functions and so forth). When using MS-DOS, BIOS services could be accessed by an application program (or by MS-DOS) by executing an INT 13h interrupt instruction to access disk functions, or by executing one of a number of other documented BIOS interrupt calls to access video display, keyboard, cassette, and other device functions.
Operating systems and executive software that are designed to supersede this basic firmware functionality provide replacement software interfaces to application software. Applications can also provide these services to themselves. This began even in the 1980s under MS-DOS, when programmers observed that using the BIOS video services for graphics display were very slow. To increase the speed of screen output, many programs bypassed the BIOS and programmed the video display hardware directly. Other graphics programmers, particularly but not exclusively in the demoscene, observed that there were technical capabilities of the PC display adapters that were not supported by the IBM BIOS and could not be taken advantage of without circumventing it. Since the AT-compatible BIOS ran in Intel real mode, operating systems that ran in protected mode on 286 and later processors required hardware device drivers compatible with protected mode operation to replace BIOS services.
In modern PCs running modern operating systems (such as Windows and Linux) the BIOS interrupt calls are used only during booting and initial loading of operating systems. Before the operating system's first graphical screen is displayed, input and output are typically handled through BIOS. A boot menu such as the textual menu of Windows, which allows users to choose an operating system to boot, to boot into the safe mode, or to use the last known good configuration, is displayed through BIOS and receives keyboard input through BIOS.[6]
Many modern PCs can still boot and run legacy operating systems such as MS-DOS or DR-DOS that rely heavily on BIOS for their console and disk I/O, providing that the system has a BIOS, or a CSM-capable UEFI firmware.
Processor microcode updates
editIntel processors have reprogrammable microcode since the P6 microarchitecture.[25][26][27] AMD processors have reprogrammable microcode since the K7 microarchitecture. The BIOS contain patches to the processor microcode that fix errors in the initial processor microcode; microcode is loaded into processor's SRAM so reprogramming is not persistent, thus loading of microcode updates is performed each time the system is powered up. Without reprogrammable microcode, an expensive processor swap would be required;[28] for example, the Pentium FDIV bug became an expensive fiasco for Intel as it required a product recall because the original Pentium processor's defective microcode could not be reprogrammed. Operating systems can update main processor microcode also.[29][30]
Identification
editSome BIOSes contain a software licensing description table (SLIC), a digital signature placed inside the BIOS by the original equipment manufacturer (OEM), for example Dell. The SLIC is inserted into the ACPI data table and contains no active code.[31][32]
Computer manufacturers that distribute OEM versions of Microsoft Windows and Microsoft application software can use the SLIC to authenticate licensing to the OEM Windows Installation disk and system recovery disc containing Windows software. Systems with a SLIC can be preactivated with an OEM product key, and they verify an XML formatted OEM certificate against the SLIC in the BIOS as a means of self-activating (see System Locked Preinstallation, SLP). If a user performs a fresh install of Windows, they will need to have possession of both the OEM key (either SLP or COA) and the digital certificate for their SLIC in order to bypass activation.[31] This can be achieved if the user performs a restore using a pre-customised image provided by the OEM. Power users can copy the necessary certificate files from the OEM image, decode the SLP product key, then perform SLP activation manually.
Overclocking
editSome BIOS implementations allow overclocking, an action in which the CPU is adjusted to a higher clock rate than its manufacturer rating for guaranteed capability. Overclocking may, however, seriously compromise system reliability in insufficiently cooled computers and generally shorten component lifespan. Overclocking, when incorrectly performed, may also cause components to overheat so quickly that they mechanically destroy themselves.[33]
Modern use
editSome older operating systems, for example MS-DOS, rely on the BIOS to carry out most input/output tasks within the PC.[34]
Calling real mode BIOS services directly is inefficient for protected mode (and long mode) operating systems. BIOS interrupt calls are not used by modern multitasking operating systems after they initially load.
In the 1990s, BIOS provided some protected mode interfaces for Microsoft Windows and Unix-like operating systems, such as Advanced Power Management (APM), Plug and Play BIOS, Desktop Management Interface (DMI), VESA BIOS Extensions (VBE), e820 and MultiProcessor Specification (MPS). Starting from the year 2000, most BIOSes provide ACPI, SMBIOS, VBE and e820 interfaces for modern operating systems.[35][36][37][38][39]
After operating systems load, the System Management Mode code is still running in SMRAM. Since 2010, BIOS technology is in a transitional process toward UEFI.[8]
Configuration
editSetup utility
editHistorically, the BIOS in the IBM PC and XT had no built-in user interface. The BIOS versions in earlier PCs (XT-class) were not software configurable; instead, users set the options via DIP switches on the motherboard. Later computers, including all IBM-compatibles with 80286 CPUs, had a battery-backed nonvolatile BIOS memory (CMOS RAM chip) that held BIOS settings.[40] These settings, such as video-adapter type, memory size, and hard-disk parameters, could only be configured by running a configuration program from a disk, not built into the ROM. A special "reference diskette" was inserted in an IBM AT to configure settings such as memory size.
Early BIOS versions did not have passwords or boot-device selection options. The BIOS was hard-coded to boot from the first floppy drive, or, if that failed, the first hard disk. Access control in early AT-class machines was by a physical keylock switch (which was not hard to defeat if the computer case could be opened). Anyone who could switch on the computer could boot it.[citation needed]
Later, 386-class computers started integrating the BIOS setup utility in the ROM itself, alongside the BIOS code; these computers usually boot into the BIOS setup utility if a certain key or key combination is pressed, otherwise the BIOS POST and boot process are executed.
A modern BIOS setup utility has a text user interface (TUI) or graphical user interface (GUI) accessed by pressing a certain key on the keyboard when the PC starts. Usually, the key is advertised for short time during the early startup, for example "Press DEL to enter Setup". The actual key depends on specific hardware. Features present in the BIOS setup utility typically include:
- Configuring, enabling and disabling the hardware components
- Setting the system time
- Setting the boot order
- Setting various passwords, such as a password for securing access to the BIOS user interface and preventing malicious users from booting the system from unauthorized portable storage devices, or a password for booting the system
Hardware monitoring
editA modern BIOS setup screen often features a PC Health Status or a Hardware Monitoring tab, which directly interfaces with a Hardware Monitor chip of the mainboard.[41] This makes it possible to monitor CPU and chassis temperature, the voltage provided by the power supply unit, as well as monitor and control the speed of the fans connected to the motherboard.
Once the system is booted, hardware monitoring and computer fan control is normally done directly by the Hardware Monitor chip itself, which can be a separate chip, interfaced through I²C or SMBus, or come as a part of a Super I/O solution, interfaced through Industry Standard Architecture (ISA) or Low Pin Count (LPC).[42] Some operating systems, like NetBSD with envsys and OpenBSD with sysctl hw.sensors, feature integrated interfacing with hardware monitors.
However, in some circumstances, the BIOS also provides the underlying information about hardware monitoring through ACPI, in which case, the operating system may be using ACPI to perform hardware monitoring.[43][44]
Reprogramming
editIn modern PCs the BIOS is stored in rewritable EEPROM or NOR flash memory, allowing the contents to be replaced and modified. This rewriting of the contents is sometimes termed flashing. It can be done by a special program, usually provided by the system's manufacturer, or at POST, with a BIOS image in a hard drive or USB flash drive. A file containing such contents is sometimes termed "a BIOS image". A BIOS might be reflashed in order to upgrade to a newer version to fix bugs or provide improved performance or to support newer hardware.
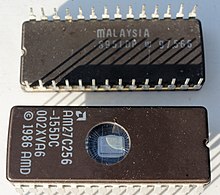
Hardware
editThe original IBM PC BIOS (and cassette BASIC) was stored on mask-programmed read-only memory (ROM) chips in sockets on the motherboard. ROMs could be replaced, but not altered, by users. To allow for updates, many compatible computers used re-programmable BIOS memory devices such as EPROM, EEPROM and later flash memory (usually NOR flash) devices. According to Robert Braver, the president of the BIOS manufacturer Micro Firmware, Flash BIOS chips became common around 1995 because the electrically erasable PROM (EEPROM) chips are cheaper and easier to program than standard ultraviolet erasable PROM (EPROM) chips. Flash chips are programmed (and re-programmed) in-circuit, while EPROM chips need to be removed from the motherboard for re-programming.[45] BIOS versions are upgraded to take advantage of newer versions of hardware and to correct bugs in previous revisions of BIOSes.[46]
Beginning with the IBM AT, PCs supported a hardware clock settable through BIOS. It had a century bit which allowed for manually changing the century when the year 2000 happened. Most BIOS revisions created in 1995 and nearly all BIOS revisions in 1997 supported the year 2000 by setting the century bit automatically when the clock rolled past midnight, 31 December 1999.[47]
The first flash chips were attached to the ISA bus. Starting in 1998, the BIOS flash moved to the LPC bus, following a new standard implementation known as "firmware hub" (FWH). In 2005, the BIOS flash memory moved to the SPI bus.[48]
The size of the BIOS, and the capacity of the ROM, EEPROM, or other media it may be stored on, has increased over time as new features have been added to the code; BIOS versions now exist with sizes up to 32 megabytes. For contrast, the original IBM PC BIOS was contained in an 8 KB mask ROM. Some modern motherboards are including even bigger NAND flash memory ICs on board which are capable of storing whole compact operating systems, such as some Linux distributions. For example, some ASUS notebooks included Splashtop OS embedded into their NAND flash memory ICs.[49] However, the idea of including an operating system along with BIOS in the ROM of a PC is not new; in the 1980s, Microsoft offered a ROM option for MS-DOS, and it was included in the ROMs of some PC clones such as the Tandy 1000 HX.
Another type of firmware chip was found on the IBM PC AT and early compatibles. In the AT, the keyboard interface was controlled by a microcontroller with its own programmable memory. On the IBM AT, that was a 40-pin socketed device, while some manufacturers used an EPROM version of this chip which resembled an EPROM. This controller was also assigned the A20 gate function to manage memory above the one-megabyte range; occasionally an upgrade of this "keyboard BIOS" was necessary to take advantage of software that could use upper memory.[citation needed]
The BIOS may contain components such as the Memory Reference Code (MRC), which is responsible for the memory initialization (e.g. SPD and memory timings initialization).[50]: 8 [51]
Modern BIOS[52] includes Intel Management Engine or AMD Platform Security Processor firmware.
Vendors and products
edit| Company | AwardBIOS | AMIBIOS | Insyde | SeaBIOS |
|---|---|---|---|---|
| License | Proprietary | Proprietary | Proprietary | LGPL v3 |
| Maintained / developed | Terminated | Terminated | Terminated | Yes |
| 32-bit PCI BIOS calls | Yes | Yes | Yes | Yes |
| AHCI | Yes | Yes | Yes | Yes |
| APM | Yes | Yes | Yes (1.2) | Yes (1.2) |
| BBS | Yes | Yes | Yes | Yes |
| Boot menu | Yes | Yes | Yes | Yes |
| Compression | Yes (LHA[53]) | Yes (LHA) | Yes (RLE) | Yes (LZMA) |
| CMOS | Yes | Yes | Yes | Yes |
| EDD | Yes | Yes | Yes | Yes |
| ESCD | Yes | Yes | ? | No |
| Flash from ROM | ? | Yes | ? | No |
| Language | Assembly | Assembly | Assembly | C |
| LBA | Yes (48) | Yes (48) | Yes | Yes (48) |
| MultiProcessor Specification | Yes | Yes | Yes | Yes |
| Option ROM | Yes | Yes | Yes | Yes |
| Password | Yes | Yes | Yes | No |
| PMM | ? | Yes | ? | Yes |
| Setup screen | Yes | Yes | Yes | No |
| SMBIOS | Yes | Yes | Yes | Yes |
| Splash screen | Yes (EPA)[54] | Yes (PCX) | Yes | Yes (BMP, JPG) |
| TPM | Unknown | Unknown | Unknown | Some |
| USB booting | Yes | Yes | Yes | Yes |
| USB hub | ? | ? | ? | Yes |
| USB keyboard | Yes | Yes | Yes | Yes |
| USB mouse | Yes | Yes | Yes | Yes |
IBM published the entire listings of the BIOS for its original PC, PC XT, PC AT, and other contemporary PC models, in an appendix of the IBM PC Technical Reference Manual for each machine type. The effect of the publication of the BIOS listings is that anyone can see exactly what a definitive BIOS does and how it does it.
In May 1984 Phoenix Software Associates released its first ROM-BIOS, which enabled OEMs to build essentially fully compatible clones without having to reverse-engineer the IBM PC BIOS themselves, as Compaq had done for the Portable, helping fuel the growth in the PC-compatibles industry and sales of non-IBM versions of DOS.[55] The first American Megatrends (AMI) BIOS was released in 1986.
New standards grafted onto the BIOS are usually without complete public documentation or any BIOS listings. As a result, it is not as easy to learn the intimate details about the many non-IBM additions to BIOS as about the core BIOS services.
Many PC motherboard suppliers licensed the BIOS "core" and toolkit from a commercial third party, known as an "independent BIOS vendor" or IBV. The motherboard manufacturer then customized this BIOS to suit its own hardware. For this reason, updated BIOSes are normally obtained directly from the motherboard manufacturer. Major IBVs included American Megatrends (AMI), Insyde Software, Phoenix Technologies, and Byosoft. Microid Research and Award Software were acquired by Phoenix Technologies in 1998; Phoenix later phased out the Award brand name (although Award Software is still credited in newer AwardBIOS versions and in UEFI firmwares).[when?] General Software, which was also acquired by Phoenix in 2007, sold BIOS for embedded systems based on Intel processors.
Open-source BIOS firmware
editThe open-source community increased their effort to develop a replacement for proprietary BIOSes and their future incarnations with an open-sourced counterparts. Open Firmware was an early attempt to make open source standard for booting firmware. It was initially endorsed by IEEE in its IEEE 1275-1994 standard but was withdrawn in 2005.[56][57] Later examples include the libreboot, coreboot and OpenBIOS/Open Firmware projects. AMD provided product specifications for some chipsets, and Google is sponsoring the project. Motherboard manufacturer Tyan offers coreboot next to the standard BIOS with their Opteron line of motherboards.
Security
editThis section needs additional citations for verification. (March 2019) |
EEPROM and Flash memory chips are advantageous because they can be easily updated by the user; it is customary for hardware manufacturers to issue BIOS updates to upgrade their products, improve compatibility and remove bugs. However, this advantage had the risk that an improperly executed or aborted BIOS update could render the computer or device unusable. To avoid these situations, more recent BIOSes use a "boot block"; a portion of the BIOS which runs first and must be updated separately. This code verifies if the rest of the BIOS is intact (using hash checksums or other methods) before transferring control to it. If the boot block detects any corruption in the main BIOS, it will typically warn the user that a recovery process must be initiated by booting from removable media (floppy, CD or USB flash drive) so the user can try flashing the BIOS again. Some motherboards have a backup BIOS (sometimes referred to as DualBIOS boards) to recover from BIOS corruptions.
There are at least five known viruses that attack the BIOS. Two of which were for demonstration purposes. The first one found in the wild was Mebromi, targeting Chinese users.
The first BIOS virus was BIOS Meningitis, which instead of erasing BIOS chips it infected them. BIOS Meningitis was relatively harmless, compared to a virus like CIH.
The second BIOS virus was CIH, also known as the "Chernobyl Virus", which was able to erase flash ROM BIOS content on compatible chipsets. CIH appeared in mid-1998 and became active in April 1999. Often, infected computers could no longer boot, and people had to remove the flash ROM IC from the motherboard and reprogram it. CIH targeted the then-widespread Intel i430TX motherboard chipset and took advantage of the fact that the Windows 9x operating systems, also widespread at the time, allowed direct hardware access to all programs.
Modern systems are not vulnerable to CIH because of a variety of chipsets being used which are incompatible with the Intel i430TX chipset, and also other flash ROM IC types. There is also extra protection from accidental BIOS rewrites in the form of boot blocks which are protected from accidental overwrite or dual and quad BIOS equipped systems which may, in the event of a crash, use a backup BIOS. Also, all modern operating systems such as FreeBSD, Linux, macOS, Windows NT-based Windows OS like Windows 2000, Windows XP and newer, do not allow user-mode programs to have direct hardware access using a hardware abstraction layer.[58]
As a result, as of 2008, CIH has become essentially harmless, at worst causing annoyance by infecting executable files and triggering antivirus software. Other BIOS viruses remain possible, however;[59] since most Windows home users without Windows Vista/7's UAC run all applications with administrative privileges, a modern CIH-like virus could in principle still gain access to hardware without first using an exploit.[citation needed] The operating system OpenBSD prevents all users from having this access and the grsecurity patch for the Linux kernel also prevents this direct hardware access by default, the difference being an attacker requiring a much more difficult kernel level exploit or reboot of the machine.[citation needed]
The third BIOS virus was a technique presented by John Heasman, principal security consultant for UK-based Next-Generation Security Software. In 2006, at the Black Hat Security Conference, he showed how to elevate privileges and read physical memory, using malicious procedures that replaced normal ACPI functions stored in flash memory.[60]
The fourth BIOS virus was a technique called "Persistent BIOS infection." It appeared in 2009 at the CanSecWest Security Conference in Vancouver, and at the SyScan Security Conference in Singapore. Researchers Anibal Sacco[61] and Alfredo Ortega, from Core Security Technologies, demonstrated how to insert malicious code into the decompression routines in the BIOS, allowing for nearly full control of the PC at start-up, even before the operating system is booted. The proof-of-concept does not exploit a flaw in the BIOS implementation, but only involves the normal BIOS flashing procedures. Thus, it requires physical access to the machine, or for the user to be root. Despite these requirements, Ortega underlined the profound implications of his and Sacco's discovery: "We can patch a driver to drop a fully working rootkit. We even have a little code that can remove or disable antivirus."[62]
Mebromi is a trojan which targets computers with AwardBIOS, Microsoft Windows, and antivirus software from two Chinese companies: Rising Antivirus and Jiangmin KV Antivirus.[63][64][65] Mebromi installs a rootkit which infects the Master boot record.
In a December 2013 interview with 60 Minutes, Deborah Plunkett, Information Assurance Director for the US National Security Agency claimed the NSA had uncovered and thwarted a possible BIOS attack by a foreign nation state, targeting the US financial system.[66] The program cited anonymous sources alleging it was a Chinese plot.[66] However follow-up articles in The Guardian,[67] The Atlantic,[68] Wired[69] and The Register[70] refuted the NSA's claims.
Newer Intel platforms have Intel Boot Guard (IBG) technology enabled, this technology will check the BIOS digital signature at startup, and the IBG public key is fused into the PCH. End users can't disable this function.
Alternatives and successors
editUnified Extensible Firmware Interface (UEFI) supplements the BIOS in many new machines. Initially written for the Intel Itanium architecture, UEFI is now available for x86 and Arm platforms; the specification development is driven by the Unified EFI Forum, an industry Special Interest Group. EFI booting has been supported in only Microsoft Windows versions supporting GPT,[71] the Linux kernel 2.6.1 and later, and macOS on Intel-based Macs.[72] As of 2014[update], new PC hardware predominantly ships with UEFI firmware. The architecture of the rootkit safeguard can also prevent the system from running the user's own software changes, which makes UEFI controversial as a legacy BIOS replacement in the open hardware community. Also, Windows 11 requires UEFI to boot,[73] with the exception of IoT Enterprise editions of Windows 11.[7]
Other alternatives to the functionality of the "Legacy BIOS" in the x86 world include coreboot and libreboot.
Some servers and workstations use a platform-independent Open Firmware (IEEE-1275) based on the Forth programming language; it is included with Sun's SPARC computers, IBM's RS/6000 line, and other PowerPC systems such as the CHRP motherboards, along with the x86-based OLPC XO-1.
As of at least 2015, Apple has removed legacy BIOS support from MacBook Pro computers. As such the BIOS utility no longer supports the legacy option, and prints "Legacy mode not supported on this system".
In 2017, Intel announced that it would remove legacy BIOS support by 2020. Since 2019, new Intel platform OEM PCs no longer support the legacy option.
See also
edit- Double boot
- Extended System Configuration Data (ESCD)
- Input/Output Control System
- ACPI (Advanced Configuration and Power Interface)
- Ralf Brown's Interrupt List (RBIL) – interrupts, calls, interfaces, data structures, memory and port addresses, and processor opcodes for the x86 architecture
- System Management BIOS (SMBIOS)
- UEFI (Unified Extensible Firmware Interface)
- Das U-Boot, often used on embedded systems
Notes
edit- ^ Although the term BIOS predates 1981, the standard for IBM PC compatible computers started with the release of the original IBM Personal Computer.
- ^ The signature at offset
+0x1FEin boot sectors is0x55 0xAA, that is0x55at offset+0x1FEand0xAAat offset+0x1FF. Since little-endian representation must be assumed in the context of IBM PC compatible machines, this can be written as 16-bit word0xAA55in programs for x86 processors (note the swapped order), whereas it would have to be written as0x55AAin programs for other CPU architectures using a big-endian representation. Since this has been mixed up numerous times in books and even in original Microsoft reference documents, this article uses the offset-based byte-wise on-disk representation to avoid any possible misinterpretation.
References
edit- ^ "Ref — System BIOS". PCGuide. Archived from the original on 2014-12-21. Retrieved 2014-12-06.
- ^ "Unified Extensible Firmware Interface". Intel.
- ^ "UEFI". OSDev.org.
- ^ a b c Kildall, Gary Arlen (June 1975), CP/M 1.1 or 1.2 BIOS and BDOS for Lawrence Livermore Laboratories
- ^ a b c Kildall, Gary Arlen (January 1980). "The History of CP/M - The Evolution of an Industry: One Person's Viewpoint" (Vol. 5, No. 1, Number 41 ed.). Dr. Dobb's Journal of Computer Calisthenics & Orthodontia. pp. 6–7. Archived from the original on 2016-11-24. Retrieved 2013-06-03.
- ^ a b "Booting · Linux Inside". 0xax.gitbooks.io. Retrieved 2020-11-10.
- ^ a b "Minimum System Requirements for Windows IoT Enterprise". Microsoft Learn. 2024-05-22. Retrieved 2024-06-07.
- ^ a b Bradley, Tony. "R.I.P. BIOS: A UEFI Primer". PCWorld. Archived from the original on 2014-01-27. Retrieved 2014-01-27.
- ^ "Removal of Legacy Boot Support for Intel Platforms Technical Advisory". Retrieved 2024-07-25.
{{cite web}}: CS1 maint: url-status (link) - ^ Swaine, Michael (1997-04-01). "Gary Kildall and Collegial Entrepreneurship". Dr. Dobb's Journal. Archived from the original on 2007-01-24. Retrieved 2006-11-20.
- ^ a b "IEEE Milestone in Electrical Engineering and Computing - CP/M - Microcomputer Operating System, 1974" (PDF). Computer History Museum. 2014-04-25. Archived (PDF) from the original on 2019-04-03. Retrieved 2019-04-03.
- ^ Shustek, Len (2016-08-02). "In His Own Words: Gary Kildall". Remarkable People. Computer History Museum. Archived from the original on 2016-12-17.
- ^ Killian, A. Joseph "Joe" (2001). "Gary Kildall's CP/M: Some early CP/M history - 1976-1977". Thomas "Todd" Fischer, IMSAI. Archived from the original on 2012-12-29. Retrieved 2013-06-03.
- ^ Fraley, Bob; Spicer, Dag (2007-01-26). "Oral History of Joseph Killian, Interviewed by: Bob Fraley, Edited by: Dag Spicer, Recorded: January 26, 2007, Mountain View, California, CHM Reference number: X3879.2007" (PDF). Computer History Museum. Archived from the original (PDF) on 2014-07-14. Retrieved 2013-06-03.
- ^ Glass, Brett (1989). "The IBM PC BIOS". Byte: 303–310. Retrieved 2021-12-31.
- ^ "HP BIOS Configuration Utility". Hewlett-Packard. 2013. Archived from the original on 2015-01-12. Retrieved 2015-01-12.
- ^ See Intel 64 and IA-32 Architectures Software Developer's Manual Archived 2012-01-26 at the Wayback Machine, volume 3, section 9.1.2
- ^ page 5-27 IBM Personal Computer Hardware Reference Library Technical Reference, 1984, publication number 6361459
- ^ "IBM 5162 PC XT286 TechRef 68X2537 Technical Reference manual" (PDF). August 1986. p. 35 (System BIOS A-5). Archived (PDF) from the original on 2014-12-11. Retrieved 2014-12-11.
- ^ How StuffWorks: What BIOS Does Archived 2008-02-07 at the Wayback Machine.
- ^ Akeljic, Bekir (2017-01-01). "BIOS BASIC INPUT/ OUTPUT SYSTEM BIOS FUNCTIONS AND MODIFICATIONS". BIOS: 12. Archived from the original on 2022-08-08. Retrieved 2022-08-08 – via INTERNATIONAL UNIVERSITY TRAVNIKFACULITY OF INFORMATION TECHNOLOGY TRAVNIKSOFTWARE PROGRAMMING.
- ^ "BIOS - CodeDocs". codedocs.org. Retrieved 2022-08-08.
- ^ "Memory Layout and Memory Map". flint.cs.yale.edu. Retrieved 2022-08-08.
- ^ "BIOS Data ACPI Table (BDAT)" (PDF). Interface Specification. 4 (5): 67. 2020. Archived (PDF) from the original on 2021-07-03. Retrieved 2022-08-08.
- ^ Stiller, Andreas; Paul, Matthias R. (1996-05-12). "Prozessorgeflüster". c't – magazin für computertechnik. Trends & News / aktuell - Prozessoren (in German). Vol. 1996, no. 6. Verlag Heinz Heise GmbH & Co KG. p. 20. ISSN 0724-8679. Archived from the original on 2017-08-28. Retrieved 2017-08-28.
- ^ Mueller, Scott (2001-06-08). Processor Update Feature | Microprocessor Types and Specifications. InformIT. Archived from the original on 2014-04-16. Retrieved 2014-04-15.
- ^ "Linux* Processor Microcode Data File". Download Center. Downloadcenter.intel.com. 2009-09-23. Archived from the original on 2014-04-16. Retrieved 2014-04-15.
- ^ Scott Mueller, Upgrading and repairing PCs 15th edition, Que Publishing, 2003 ISBN 0-7897-2974-1, pages 109-110
- ^ "KB4100347: Intel microcode updates". support.microsoft.com. Retrieved 2020-09-20.
- ^ "Microcode - Debian Wiki". wiki.debian.org. Retrieved 2020-09-19.
- ^ a b "How SLP and SLIC Works". guytechie.com. 2010-02-25. Archived from the original on 2015-02-03. Retrieved 2015-02-03.
- ^ "Create and add an OEM ACPI SLIC table module to a congatec BIOS" (PDF). congatec.com. 2011-06-16. Archived (PDF) from the original on 2014-08-02. Retrieved 2015-02-03.
- ^ Whitson Gordon (2014-01-13). "A Beginner's Introduction to Overclocking Your Intel Processor". Lifehacker. Gawker Media. Archived from the original on 2014-12-07. Retrieved 2014-12-06.
- ^ Smart Computing Article - What Is The BIOS? Archived 2012-03-10 at the Wayback Machine - Computing Basics July 1994 • Vol.5 Issue 7
- ^ "What is ACPI (Advanced Configuration and Power Interface)? - Definition from WhatIs.com". SearchWindowsServer. Retrieved 2020-09-18.
- ^ "Changing hardware abstraction layer in Windows 2000 / XP – Smallvoid.com". 2001-01-15. Retrieved 2020-09-18.
- ^ "What is ACPI?". www.spo-comm.de. Retrieved 2020-09-18.
- ^ lorihollasch. "Support for headless systems - Windows drivers". docs.microsoft.com. Retrieved 2020-12-05.
- ^ "Memory Map (x86) - OSDev Wiki". wiki.osdev.org. Retrieved 2020-12-11.
- ^ Torres, Gabriel (2004-11-24). "Introduction and Lithium Battery". Replacing the Motherboard Battery. hardwaresecrets.com. Archived from the original on 2013-12-24. Retrieved 2013-06-20.
- ^ Constantine A. Murenin (2010-05-21). "11.1. Interfacing from the BIOS". OpenBSD Hardware Sensors – Environmental Monitoring and Fan Control (MMath thesis). University of Waterloo: UWSpace. hdl:10012/5234. Document ID: ab71498b6b1a60ff817b29d56997a418.
- ^ Constantine A. Murenin (2007-04-17). "2. Hardware review". Generalised Interfacing with Microprocessor System Hardware Monitors. Proceedings of 2007 IEEE International Conference on Networking, Sensing and Control, 15–17 April 2007. London, United Kingdom: IEEE. pp. 901–906. doi:10.1109/ICNSC.2007.372901. ISBN 978-1-4244-1076-7. IEEE ICNSC 2007, pp. 901—906.
- ^ "aibs – ASUSTeK AI Booster ACPI ATK0110 voltage, temperature and fan sensor". OpenBSD, DragonFly BSD, NetBSD and FreeBSD. 2010.
- ^ "acpi_thermal(4)". www.freebsd.org. Retrieved 2021-02-24.
- ^ "Decoding RAM & ROM Archived 2012-04-06 at the Wayback Machine." Smart Computing. June 1997. Volume 8, Issue 6.
- ^ "Upgrading Your Flash BIOS For Plug And Play Archived 2012-04-06 at the Wayback Machine." Smart Computing. March 1996. Volume 7, Issue 3.
- ^ "Time To Check BIOS Archived 2011-07-16 at the Wayback Machine." Smart Computing. April 1999. Volume 7, Issue 4.
- ^ "Archived copy". Archived from the original on 2021-08-18. Retrieved 2021-04-01.
{{cite web}}: CS1 maint: archived copy as title (link) - ^ "SplashTop's Instant-On Linux Desktop | Geek.com". Archived from the original on 2008-09-07.
- ^ Posted by Alex Watson, possibly repost from original content on custompc.com [unclear]. "The life and times of the modern motherboard". 2007-11-27. Archived from the original on 2012-07-24. Retrieved 2013-02-02.
- ^ David Hilber Jr. (August 2009). "Considerations for Designing an Embedded Intel Architecture System with System Memory Down" (PDF). Intel. Archived (PDF) from the original on 2012-10-18. Retrieved 2013-02-02.
- ^ "Types of BIOS". rompacks.com. Retrieved 2021-09-20.
- ^ Stiller, Andreas (2001). "Prozessor-Patches". c't (in German) (5). Heise: 240. Archived from the original on 2015-11-22. Retrieved 2015-11-21.
- ^ "Award BIOS logo". 2015-06-15. Archived from the original on 2015-12-21. Retrieved 2015-12-06.
- ^ Phoenix Eagerly Waiting to Clone Next-Generation IBM BIOS. Archived 2014-01-22 at the Wayback Machine, InfoWorld, 9 March 1987.
- ^ IEEE Standard for Boot (Initialization Configuration) Firmware: Core Requirements and Practices. 1994-10-28. pp. 1–262. doi:10.1109/IEEESTD.1994.89427. ISBN 978-0-7381-1194-0.
{{cite book}}:|journal=ignored (help) - ^ "IEEE Standards Association". IEEE Standards Association. Retrieved 2023-04-26.
- ^ "Definition of hardware abstraction layer". PCMAG. Retrieved 2022-07-11.
- ^ New BIOS Virus Withstands HDD Wipes, 27 March 2009. Marcus Yam. Tom's Hardware US
- ^ "Black Hat 2006 Multimedia - Presentation, Audio and Video Archives". www.blackhat.com. Retrieved 2019-04-21.
- ^ Sacco, Anibal; Alfredo Ortéga (2009-03-23). "Persistent BIOS Infection". Exploiting Stuff. Archived from the original on 2009-08-04. Retrieved 2010-02-06.
- ^ Fisher, Dennis. "Researchers unveil persistent BIOS attack methods". Threat Post. Archived from the original on 2010-01-30. Retrieved 2010-02-06.
- ^ Giuliani, Marco (2011-09-13). "Mebromi: the first BIOS rootkit in the wild". blog. Archived from the original on 2011-09-23. Retrieved 2011-09-19.
- ^ "360发布"BMW病毒"技术分析报告". blog. Archived from the original on 2011-09-25. Retrieved 2011-09-19.
- ^ Yuan, Liang. "Trojan.Mebromi". Threat Response. Archived from the original on 2011-09-23. Retrieved 2011-09-19.
- ^ a b "How did 60 Minutes get cameras into a spy agency?". CBS News. 2013-12-15. Archived from the original on 2014-04-22. Retrieved 2014-04-15.
- ^ Spencer Ackerman in Washington (2013-12-16). "NSA goes on 60 Minutes: the definitive facts behind CBS's flawed report". theguardian.com. Archived from the original on 2014-01-25. Retrieved 2014-01-27.
- ^ Friedersdorf, Conor (2013-12-16). "A Question for 60 Minutes: Why Would China Want to Destroy the Global Economy?". The Atlantic. Retrieved 2019-03-26.
- ^ Poulsen, Kevin (2013-12-16). "60 Minutes Puff Piece Claims NSA Saved U.S. From Cyberterrorism". Wired. ISSN 1059-1028. Retrieved 2019-03-26 – via www.wired.com.
- ^ Sharwood, Simon (2013-12-16). "NSA alleges 'BIOS plot to destroy PCs'". The Register. Retrieved 2019-03-26.
- ^ "Windows and GPT FAQ". microsoft.com. Microsoft. Archived from the original on 2011-02-19. Retrieved 2014-12-06.
- ^ "Extensible Firmware Interface (EFI) and Unified EFI (UEFI)". Intel. Archived from the original on 2010-01-05. Retrieved 2014-12-06.
- ^ "Windows 11 Specs and System Requirements | Microsoft". Microsoft. Retrieved 2021-10-14.
Further reading
edit- IBM Personal Computer Technical Reference (Revised ed.). IBM Corporation. March 1983.
- IBM Personal Computer AT Technical Reference. IBM Personal Computer Hardware Reference Library. Vol. 0, 1, 2 (Revised ed.). IBM Corporation. March 1986 [1984-03]. 1502494, 6139362, 6183310, 6183312, 6183355, 6280070, 6280099.
- Phoenix Technologies, Ltd. (1989) [1987]. System BIOS for IBM PC/XT/AT Computers and Compatibles — The Complete Guide to ROM-Based System Software. Phoenix Technical Reference Series (1st ed.). Addison Wesley Publishing Company, Inc. ISBN 0-201-51806-6.
- Phoenix Technologies, Ltd. (1989) [1987]. CBIOS for IBM PS/2 Computers and Compatibles — The Complete Guide to ROM-Based System Software for DOS. Phoenix Technical Reference Series (1st ed.). Addison Wesley Publishing Company, Inc. ISBN 0-201-51804-X.
- Phoenix Technologies, Ltd. (1989) [1987]. ABIOS for IBM PS/2 Computers and Compatibles — The Complete Guide to ROM-Based System Software for OS/2. Phoenix Technical Reference Series (1st ed.). Addison Wesley Publishing Company, Inc. ISBN 0-201-51805-8.
- Phoenix Technologies, Ltd. (June 1991). System BIOS for IBM PCs, Compatibles, and EISA Computers — The Complete Guide to ROM-Based System Software. Phoenix Technical Reference Series (2nd ed.). Amsterdam: Addison Wesley Publishing Company, Inc. ISBN 0-201-57760-7.
- BIOS Disassembly Ninjutsu Uncovered, 1st edition, a freely available book in PDF format [1]
- More Power To Firmware, free bonus chapter to the Mac OS X Internals: A Systems Approach book
External links
edit- "BIOS Boot Specification 1.01" (PDF). Phoenix.com. 1996-01-11. Archived from the original (PDF) on 2011-07-15.
- "How BIOS Works". How Stuff Works. 2000-09-06.
- "Implementing a Plug and Play BIOS Using Intel's Boot Block Flash Memory" (PDF). Intel. February 1995. Archived from the original (PDF) on 2007-11-28. Retrieved 2007-11-28.
- "List of BIOS options". techarp.com. Archived from the original on 2014-01-27.
- "Persistent BIOS Infection". Phrack. No. 66. 2009-06-01. Archived from the original on 2011-04-30. Retrieved 2011-04-30.
- "Preventing BIOS Failures Using Intel Boot Block Flash Memory" (PDF). Intel. December 1998. Archived from the original (PDF) on 2007-03-29. Retrieved 2007-03-29.